Most CTOs think copying data to an Indian region fixes RBI rules, yet audits expose hidden gaps deep in the architecture. The surprise isn’t that the audit exists; it’s that the failure shows up in places no one looked at. But there's a catch: the rule covers the entire data lifecycle, not just storage.
The Myth That Data Residency Alone Guarantees RBI Compliance

RBI’s 2018 circular tells you to store customer identifiers, payment‑sensitive data, and end‑to‑end transaction details within India. But that's not all - the rule covers capture, consent, processing, retention, and deletion. If any step happens abroad without RBI consent, the audit flags a breach.
What the law really says - Primary copy must live in an Indian region. - A foreign copy may exist only with explicit RBI consent. - That foreign copy must be erased within six months.
This is where most companies go wrong. The next step is to move beyond simple residency.
Why the ‘Move-It-In-India’ Fix Breaks Down in Real Deployments
Legacy workloads often lack the metadata needed for an audit. They were built before the RBI directive, so they don’t record who gave consent or when a copy was deleted abroad.
Teams that try to retrofit compliance discover two hard truths:
- Metadata gaps - without immutable logs, you cannot prove that a foreign copy was removed on time.
- Operational drift - adding a new region today does not automatically tag existing pipelines, batch jobs, or streaming topics.
The RBI guidelines for payment aggregators stress that data must be stored in India within six months of the directive, and that any overseas copy needs consent and a deletion schedule. A continuous compliance engine provides that missing piece.
Continuous Compliance Engine: The Insight That Saves You Audits
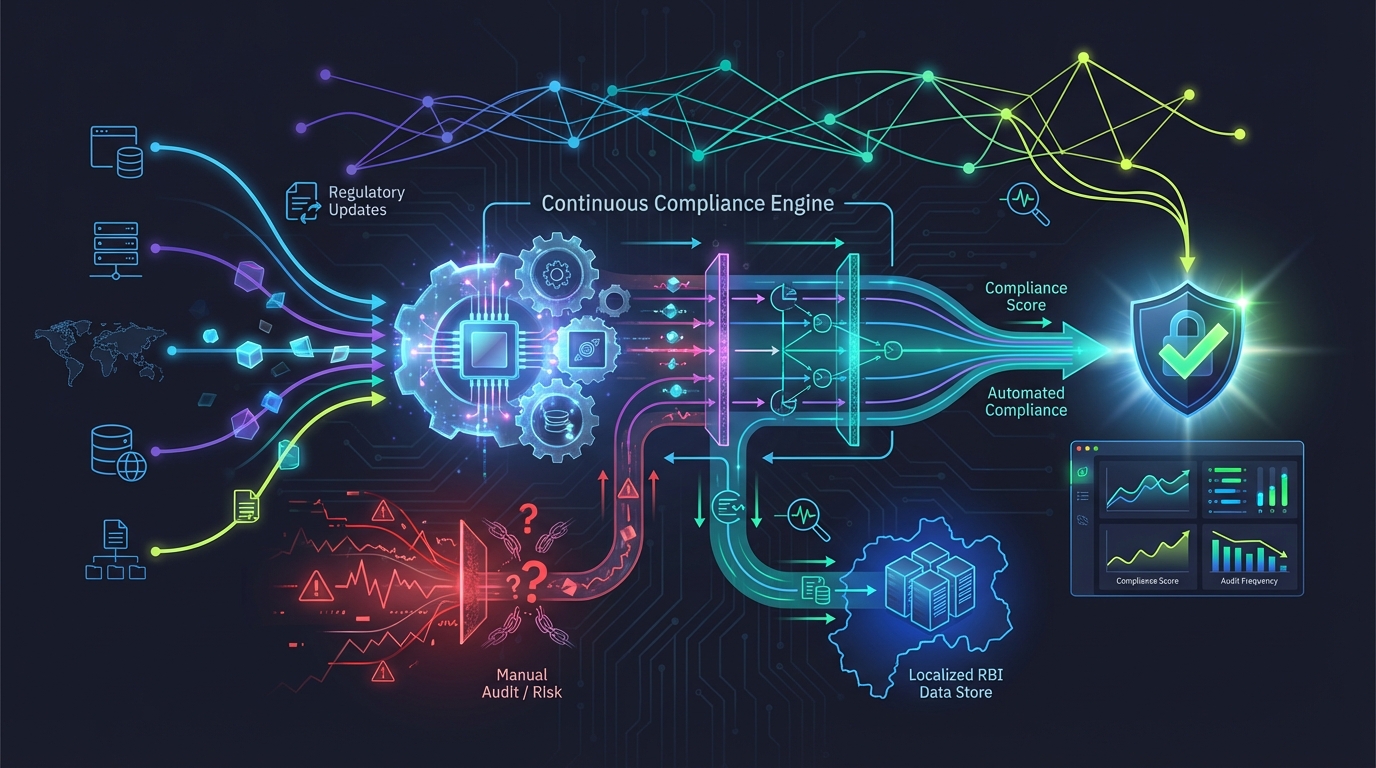
Imagine a monitor that watches every data‑access event, every consent flag, and every deletion request in real time. This engine does three things that manual processes cannot: - Collects immutable evidence on every change, creating audit‑ready snapshots automatically. - Triggers alerts when a foreign copy is created without consent, or when the six‑month deletion window is about to close. - Integrates with CI/CD pipelines, so a new microservice cannot be deployed unless it declares residency and consent policies in its manifest.
1# Example of a policy-as-code snippet for a CI pipeline2policies:3 residency: "india"4 consent_required: true5 deletion_deadline_days: 180
This turns compliance from a yearly checklist into a living guardrail. But how do you implement it?
Embedding the Engine in Your Cloud - Step‑by‑Step Blueprint
1. Provision Indian‑region resources with IaC
1# terraform/main.tf2provider "aws" {3 region = "ap-south-1" # Mumbai4}56resource "aws_s3_bucket" "payment_data" {7 bucket = "payment-data-india"8 acl = "private"9 versioning {10 enabled = true11 }12}
Run `terraform init && terraform apply`. All new buckets now sit in Mumbai. Next, you need to install the compliance SDK.
2. Install the compliance SDK via Helm
1# helm/values.yaml2complianceEngine:3 enabled: true4 region: "ap-south-1"5 policyConfigMap: "compliance-policies"
1helm repo add levitation https://charts.levitation.in2helm install compliance-sdk levitation/compliance-engine -f helm/values.yaml
The SDK injects an admission controller into the Kubernetes API server. Every pod creation is checked for residency and consent annotations. But that's still not enough.
3. Automate consent capture and six‑month deletion
1# lambda/delete_foreign_copy.py2import boto3, datetime34s3 = boto3.client('s3')5def handler(event, context):6 bucket = event['detail']['bucket']7 key = event['detail']['object']8 created = datetime.datetime.strptime(event['detail']['creationDate'], "%Y-%m-%d")9 if (datetime.datetime.utcnow() - created).days > 180:10 s3.delete_object(Bucket=bucket, Key=key)
Deploy this as an AWS Lambda (or GCP Cloud Function) triggered by S3 ObjectCreated events in any non‑Indian bucket. The function automatically removes the object after 180 days, satisfying the RBI deletion rule. Now you're getting close.
4. Run a compliance health check on legacy workloads -
1# Example scan command2kafka-topics.sh --describe --bootstrap-server broker:9092 | grep -i "replication-factor"
If any topic lacks replication across Indian brokers, the scan flags it. Finally, you need to validate the end‑to‑end flow.
5. Validate end‑to‑end flow
- Create a test payment record via the API.
- Verify it lands in the Indian S3 bucket.
- Check the compliance SDK logs for a “residency‑validated” entry.
- Simulate a foreign copy and watch the Lambda delete it after 180 days.
These steps turn a complex retrofit into a manageable rollout. The engine continuously enforces policies, so drift cannot reappear. And the payoff is tangible. The following section quantifies that payoff.
The Tangible Payoff: What Happens When You Pass RBI Audits
Passing an RBI audit does more than avoid penalties. It unlocks real business value: - Revenue stays intact - no shutdowns, no loss of transaction volume. - Board confidence soars - audit success becomes a strategic differentiator, not a footnote. - Speed to market improves - new services can be launched without a separate compliance gate each time.
Banks that have adopted a continuous‑compliance model report smoother regulator interactions and faster feature releases. Now, you can focus on growth. The FAQ below addresses the most common lingering doubts.
Frequently Asked Questions
Q: What specific data must be stored in India under RBI rules?
A: Customer identifiers, end‑to‑end transaction details, and payment‑sensitive data such as account numbers, OTPs, and PINs must reside in India. Any foreign copy is allowed only with RBI consent and must be deleted within six months.
Q: How can I prove continuous compliance during an RBI audit?
A: Deploy an automated compliance engine that logs every data‑access event, captures immutable snapshots, and generates audit‑ready reports on demand. This eliminates manual evidence collection.
Q: Is moving workloads to an Indian region enough to pass the audit?
A: No. Residency covers only storage location. RBI also requires consent management, timely deletion of foreign copies, and full lifecycle audit trails - areas many migrations overlook.
Q: What penalties does RBI impose for non‑compliance?
A: Penalties can include fines and possible suspension of payment‑system licenses, along with reputational damage.
To learn more about RBI compliance and how to implement a continuous compliance engine, visit our resource page.
